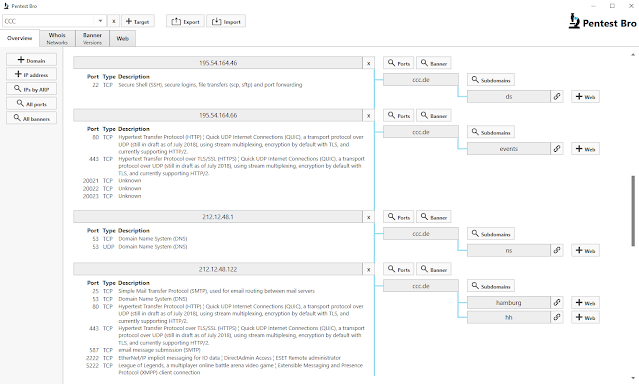
PentestBro - Combines Subdomain Scans, Whois, Port Scanning, Banner Grabbing And Web Enumeration Into One Tool - RedPacket Security

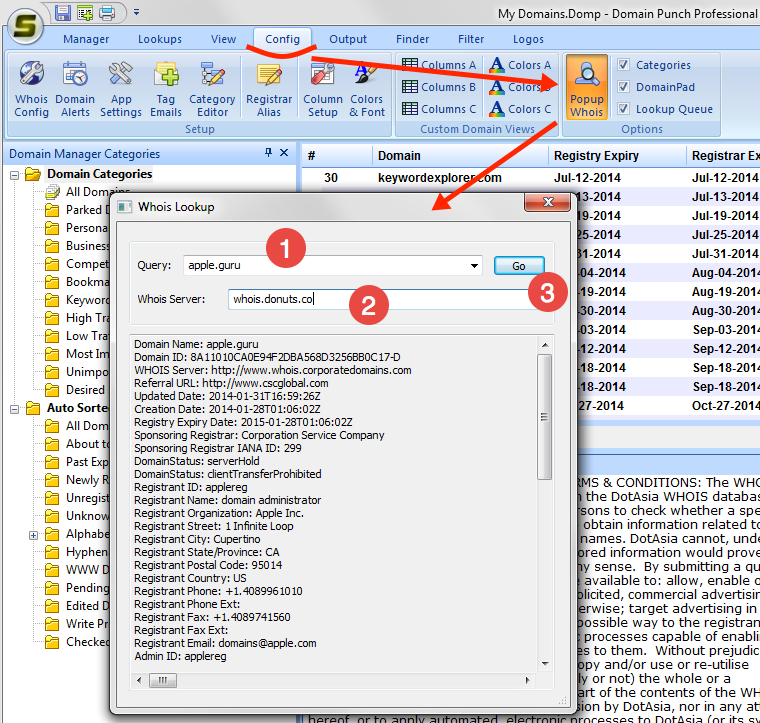
Cyber Detective🇺🇦 on Twitter: "Tenssens #osint framework Whois MD5 Cracker Subdomain finder Site Technology Lookup DNS Lookup Admin Finder HTTP Header IP Location Port Scan Robots.txt https://t.co/qQV3ke7KGd https://t.co/JU52PogKBF" / Twitter

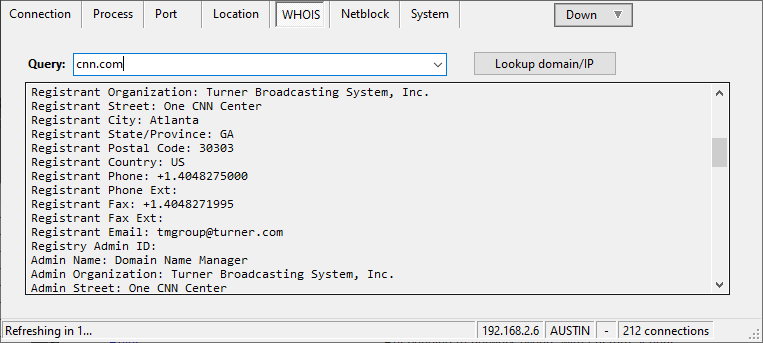
Nmap cheat sheet: From discovery to exploits, Part 3: Gathering additional information about host and network | Infosec Resources